Are you suffering from multiple username login attempts on your WordPress website? Do you need to block potential threats and stop hackers?
Website hacking and other forms of cyber terrorism have become the norm. I mean, how safe is your password from hackers?
We cannot afford business communications disruptions which is why it’s so important to do everything possible to secure your WordPress installation.
I use the free WordFence plugin and have been very happy with it.
It doesn’t slow down my site, doesn’t gobble up resources and sends a useful email digest of website security-related activity.
WordPress Weaknesses
WordPress has a massive chink in its armour. Out of the box, the default username and password are often left unchanged by the webmaster. This is a problem.
- It’s not unreasonable to say, right now, there are a few hundred thousand WordPress websites using admin and password as the login details.
Uneducated WP website creators constantly take risks with such mistakes and it’s no surprise WordPress websites are so vulnerable to attack.
- Another issue is failing to hide the login username from public view which can also increase the chances of a security breach.
I wrote about that here: You’re About to Get Hacked: A Common WordPress Mistake.
This is where WordFence comes in. Among other things, the plugin monitors these login attempts and reports it to you.
I’m pleased to say these login attempts have a 100% failure rate on my sites. No one has gotten in.
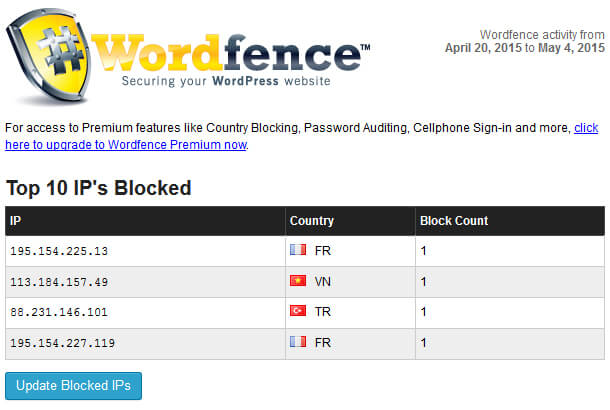
WordFence Email Digest
Once a month I receive an email roundup of my website security. I appreciate these overview stats, especially because this is a free plugin.
There are 5 sections to the digest email:
- Top 10 IP’s blocked
- Top 10 countries blocked
- Top 10 failed logins
- Recently modified files
- Updates
Let’s take a quick look at each of these.
Top 10 IP’s Blocked
The IP addresses shown in the screenshot below indicate the remote address of a hacker or a bot testing my defences.
Thankfully, my site holds up like the walls of ancient Babylon, but I’m always on guard because even the most secure sites can be compromised.
The issue I have with these IP stats is that they’re probably proxies. You see, if you have spam issues with a website, your host will usually tell you to block IP addresses as a supposed antidote to the problem.
But when you do that, the hacker bots will use an alternative IP and carry on throwing itself at your site.
Blocking IP addresses is pointless if you’re subject to large attacks. It’s usually popular sites that experience this.
For this reason I use the free reverse proxy and content delivery network CloudFlare. This acts as a shield around your entire site and reduces some of the aggro you would otherwise get with spam bots.
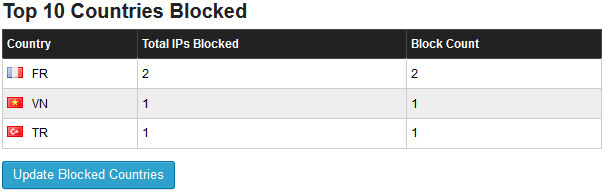
Top 10 Countries Blocked
This shows where the IPs of the hackers originated. Again, if they’re using proxies, the data is largely useless.
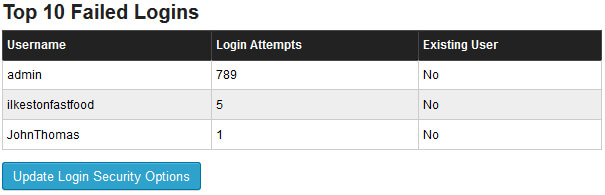
Top 10 Failed Logins
Here’s a digest email screenshot that was sent today reporting what usernames had been used over the last month trying to log in into one of my websites:
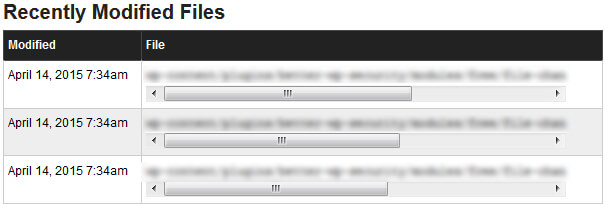
Recently Modified Files
This is a handy report because it shows what files within your WordPress installation have been changed. The screenshot below is reporting on a plugin I updated last week.
However, if someone was gaining access to my directory and injecting malicious files or making modifications, I’d want to know about it.
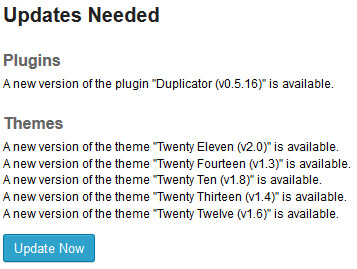
Updates Needed
Thanks to the email digest I know that the Duplicator plugin needs to be updated. This particular plugin is not vital to the running of the site so it isn’t important to update any time soon.
However, I run the Genesis Framework plugin and I would like to know as soon as that needs to be updated because it powers my site and is important.
When I get an update alert about a plugin, if I’m using that same plugin on other sites, I can log into the other sites to update the plugin even if I didn’t get email alerts for those other sites.
Daily Alerts
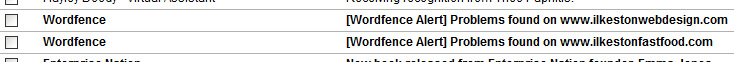
Besides the digest emails, individual emails are sent when plugins are in need of an update.
The first time I received such an email I panicked because the subject line read, “Problems found on Ilkeston Web Design.”
But it was just a reminder to update a plugin. A little dramatic calling it a “problem.”
Premium
You can upgrade to the premium version for about $39 annually but I haven’t upgraded and find the free version acceptable for lower traffic sites.
You can find out the differences between Free and Premium on the WordFence website.
Download WordFence
You can download the plugin files from this link and add to your WordPress site – https://wordpress.org/plugins/wordfence/
Alternatively go to Plugin > Add Plugin in your dashboard and search the WordPress plugin repository.
WordFence Blog
They also run a blog with security tips for webmasters. Read the WordFence blog if you’re wanting to learn more.


Add Your Thoughts